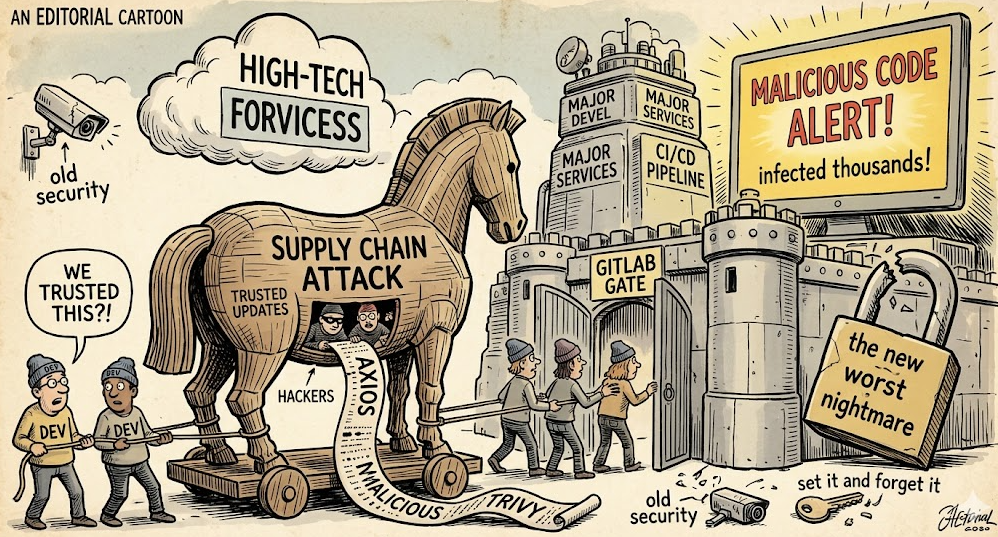
In March 2026, attackers compromised Aqua Security’s Trivy vulnerability scanner and its GitHub Actions. They force-pushed 76 of 77 tags in trivy-action to point at malicious commits that stole CI/CD secrets. The campaign, attributed to TeamPCP, also published a tainted Trivy binary v0.69.4 and later hit Checkmarx KICS and LiteLLM. Microsoft observed theft of AWS, GCP, and Azure credentials, Kubernetes secrets, and database keys, exfiltrated as encrypted archives. The attack shows how poisoning trusted automation lets one change spread to thousands of pipelines instantly.
Article:
We spent years hardening servers, then attackers walked in through the build script. The Trivy supply chain compromise in March is a textbook example of trusted automation turned against us.
On March 19, threat actors used stolen credentials to reassign 76 of 77 version tags in the aquasecurity/trivy-action repository. Any CI/CD workflow referencing those tags silently pulled attacker code on the next run.
At the same time they published a malicious Trivy binary v0.69.4 to GitHub Releases and container registries. It ran the normal scan, so pipelines looked green, while a hidden Python stealer harvested secrets in the background.
Why it matters is scope. Trivy is embedded in thousands of DevOps pipelines as a security scanner. When the scanner itself is poisoned, you are not just compromising one company, you are compromising everyone who trusts the update.
Microsoft tracked the campaign, attributed to TeamPCP, and saw it expand within days to Checkmarx KICS and LiteLLM. Each wave used a new command-and-control domain themed to the project, like scan.aquasecurtiy.org.
The technical detail is brutal in its simplicity. The stealer dumped environment variables, queried AWS IMDS and ECS metadata, read GCP service account keys, harvested Azure variables, and ran kubectl to pull all Kubernetes secrets. It also grabbed SSH logs, database strings, and even Slack webhooks.
Interestingly enough, everything was packaged into an encrypted tpcp.tar.gz and exfiltrated over HTTPS. Then the malware deleted temp files and let the legitimate Trivy scan finish, so operators saw no errors.
CrowdStrike and ARMO noted the attack abused Git’s mutable tags and spoofed commit identities, a design feature turned into a weapon. Because tags can be force-pushed, pinning to @v0.35 is not safe unless you pin to a commit SHA.
The community response has been fast but sobering. Microsoft Defender, Palo Alto Cortex, and others released detections, Aqua removed the malicious artifacts within hours, and CERT-EU confirmed data exfiltration from dozens of clients. Guidance now stresses least-privilege tokens, ephemeral runners, and pinning actions to SHAs.
But the damage model has changed. We are not talking about phishing one developer. We are talking about one compromised automation step that inherits cloud admin permissions and spreads like a worm across downstream builds.
So the era of set it and forget it for CI/CD is over. If your pipeline can deploy to production, treat the tools that run inside it with the same scrutiny you give production code. Because attackers already do.



